Publishing a Website Using Raspberry Pi as a Server
Setting up nginx on Raspberry Pi
# Install and enable nginx
sudo dnf install nginx
# Edit /etc/nginx/nginx.conf
# sudo nano /etc/nginx/nginx.conf
# Start and enable nginx
sudo systemctl start nginx
sudo systemctl enable nginx
sudo systemctl status nginx
Editing /etc/nginx/nginx.conf
Add the following inside http { server {} }:
location / {
return 200 'Hello, world!';
add_header Content-Type text/plain;
}
Cloudflare Settings
- Go to https://one.dash.cloudflare.com/.
- Open "Network" → "Tunnels".
- Click "Add a tunnel".

- Click "Select Cloudflared".

- Enter a suitable name for "Tunnel name" and click "Save tunnel".

Installing cloudflared
# Add cloudflared.repo to /etc/yum.repos.d/
curl -fsSl https://pkg.cloudflare.com/cloudflared-ascii.repo | sudo tee /etc/yum.repos.d/cloudflared.repo
sudo dnf clean packages
# Install cloudflared
sudo dnf install -y cloudflared --nogpgcheck
Starting cloudflared service
sudo cloudflared service install xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
Routing traffic
Set the hostname's subdomain and domain, service type, and URL.
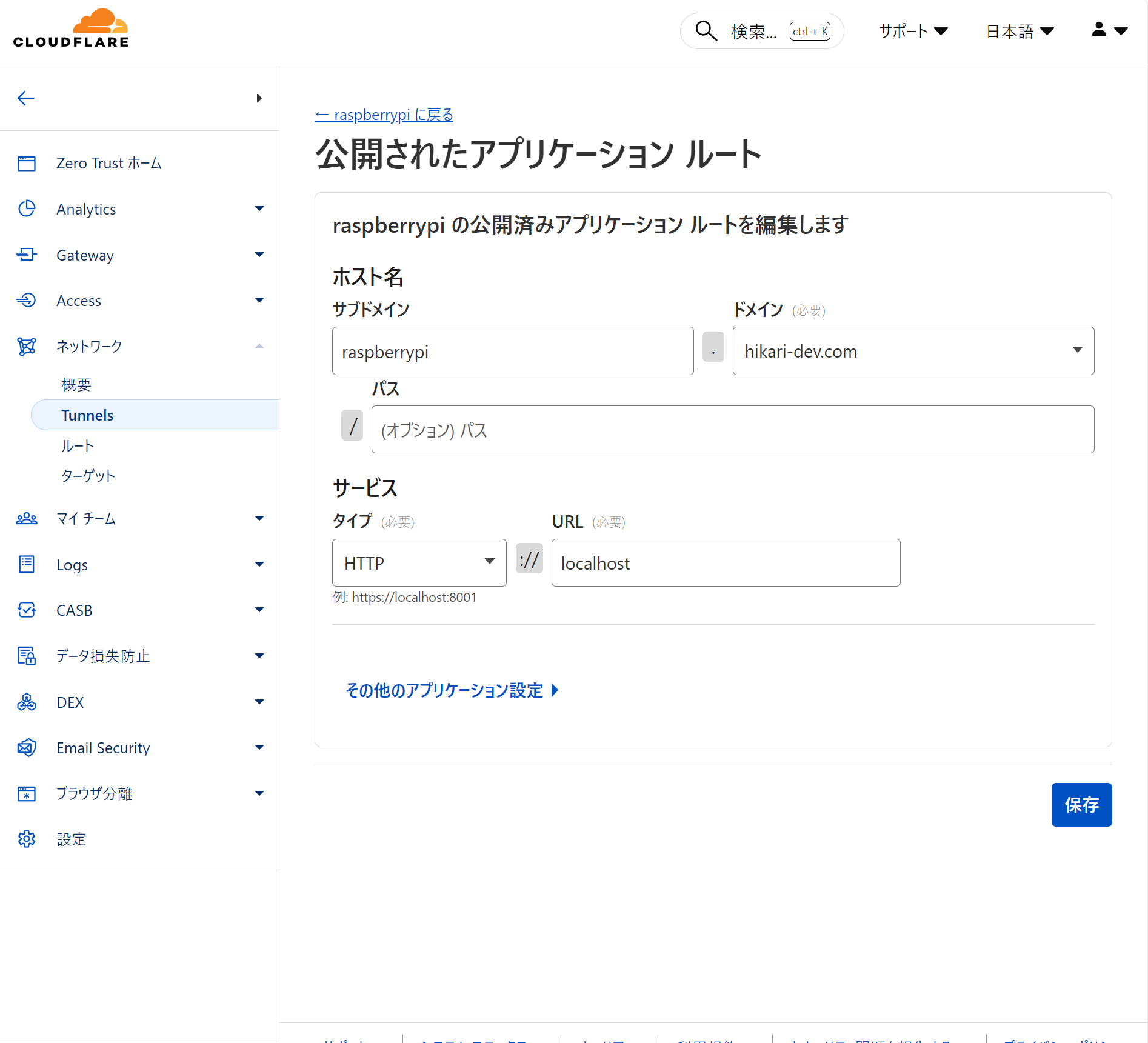
Click "Complete setup".